
Cybersecurity in the Quantum Era
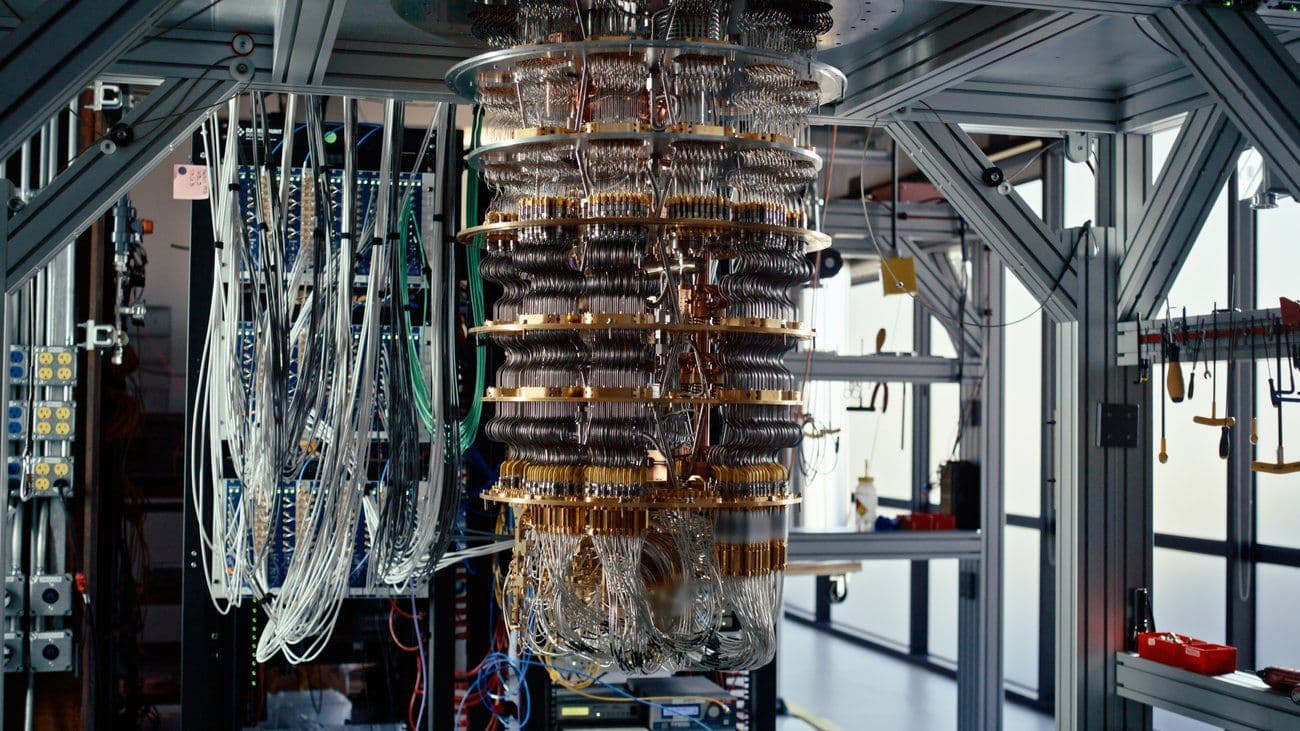
The development of quantum computing is no longer just academic research. Organizations like IBM, Google, and Microsoft continue to increase the capacity of their quantum processors. While stable, large-scale quantum computers are not yet fully operational for general use, their implications for cybersecurity are already very real. The quantum era has the potential to fundamentally change modern cryptography—the very foundation of secure digital communications, financial transactions, government systems, and critical infrastructure.
Why Does Quantum Computing Threaten Current Cryptography?
Most current digital security systems rely on public-key cryptography such as:
- RSA (large number factorization-based)
- ECC (Elliptic Curve Cryptography)
- Diffie-Hellman Key Exchange
The security of these algorithms is based on the assumption that factoring large numbers or solving discrete logarithms requires a very long computation time for classical computers.
However, quantum algorithms like Shor's Algorithm are theoretically capable of solving these problems exponentially faster. This means that:
- HTTPS encryption
- Corporate VPNs
- Digital signatures
- PKI infrastructure
could potentially become vulnerable when large-scale quantum computers become available.
Post-Quantum Cryptography (PQC) as a Solution
In response to these threats, institutions such as the National Institute of Standards and Technology (NIST) developed the Post-Quantum Cryptography (PQC) standard.
PQC is a cryptographic algorithm that:
- Resistant to classical computer attacks
- Resistant to currently known quantum algorithms
Some of the main PQC approaches:
- Lattice-based cryptography
- Hash-based signatures
- Code-based cryptography
- Multivariate polynomial cryptography
This standard is beginning to be adopted by enterprise vendors and global cloud providers.


